📜 The Origins
Back in 2019, Scott Piper started a Github repository to track changes to AWS Managed Policies. It was a simple setup, manually triggered but it worked well and was incredibly useful. Using git diff or Github.com UI, Scott and the community could easily see how policies evolved over time.
At that time, AWS didn’t publicly share the changes made to managed policies by the various “two-pizza” product teams inside AWS.
Note: If your production workloads depend on AWS-managed IAM policies, you’re adding an external dependency you don’t control. That’s risky and generally not a recommended architecture pattern. What happens if AWS removes a permission or worse, retires a policy?
A safer approach is to copy the content of an AWS-managed policy into your own IAM policy and manage it yourself, on your own timeline.
🤖 From Manual to Automated
After chatting with Scott, I created a fork of his repository with a GitHub Actions workflow and a Fargate task to run the comparison automatically every 4 hours during weekdays. Only changed policies are committed. That’s how the MAMIP project (Managed AWS Managed IAM Policies) was born. Fully automated and running 24/7.
The best part: automation came with notification channels: a Twitter Bot (X), a Bluesky account, GitHub notifications, and an SNS Topic. The goal was simple: bring AWS policy change visibility to the cloud security community, without anyone having to check GitHub manually.
Over time, I added a few tools that leverage AWS Access Analyzer to detect potential security issues within AWS-managed IAM policies.
🌐 IAMTrail: The Public Archive
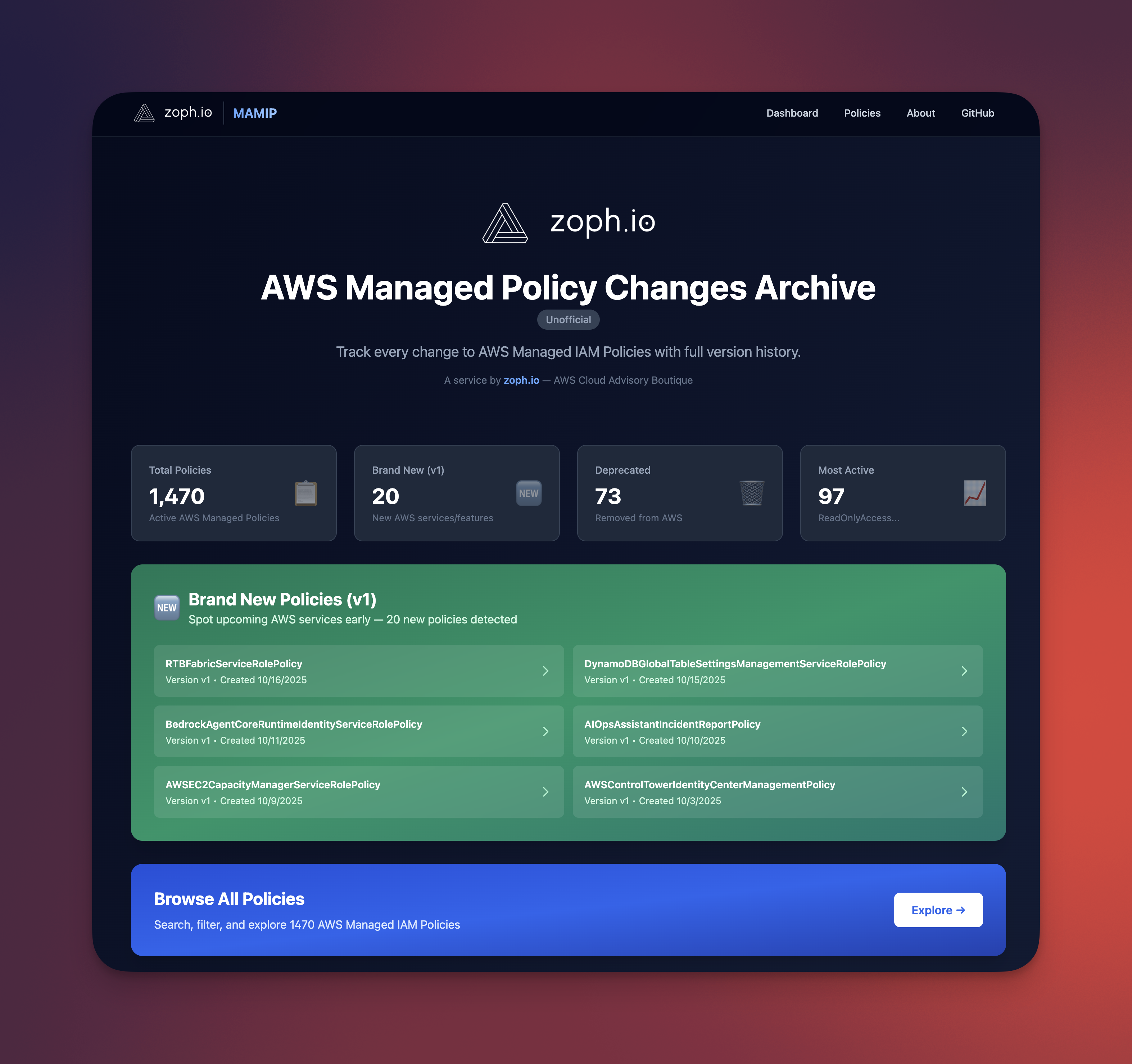
The companion experience has been reworked and rebranded as IAMTrail, with the same lineage as MAMIP but now a dedicated site for browsing and understanding managed policy history.
IAMTrail.com is a searchable archive of AWS managed IAM policies with full version history and diffs, tracked since 2019. The dashboard surfaces brand-new policies (version 1), which helps spot new AWS services or features as they ship, along with deprecated policies, most active policies, largest policies, service growth, year-over-year change velocity, lifecycle stats, and more.
Endpoint signals complement the policy archive: regions and services derived from botocore, so you can correlate API surface changes with IAM moves when it helps your analysis.
For a calmer workflow than scrolling social feeds, there are email digests (daily or weekly, with inline diffs). Pick specific policies or follow the full set through Subscribe.
📌 Conclusion
What started as MAMIP now lives on as IAMTrail: the same commitment to real-time visibility into AWS-managed IAM policy changes, with a clearer home at https://iamtrail.com. Whether you care about security drift, new launches, or keeping your own copies aligned, the archive and notifications are there to help.
That’s all, folks! 👋🏼
zoph.