
Hi Folks,
Lately, I was experimenting with GitHub Actions (GHA), as it has been a buzzword since General Availability (GA), but I didn’t take the time to try it before. I’ve done it for you folks. 🙌
Context
GHA was released on GA in November 2019, the main features are:
- Automate development workflows (CI/CD):
build,test,deploy - Hosted runners / self-hosted runners
- Automate the management of your GH Community: PR, Code Reviews, or Issue Tracking
- Built-in secrets store
My Objectives
- Replace my manually (
Makefile) deployed pet projects.
Getting Started
First of all, you will need to create your workflow at the following path: .github/workflows with YML file(s) in your GitHub repository.
First example
|
|
Now, let’s focus on my use case using SAM or Terraform.
AWS Credentials
One major step is to authenticate to your Cloud Service Provider (CSP), in my case: AWS. For security purposes, I’m using Assume Role to get least privilege authorizations on my AWS Account.
Fortunately, AWS is sharing a well-maintained GHA to get credentials tokens in your GHA Jobs.
Using Terraform
In this Terraform example, I’m using GHA to replace my manually deployed (Makefile) MAMIP bot.
Name and Event Trigger
In this section you will define the name of the GHA Workflow and the event that will trigger this workflow. In this example, it’s the git push on the master branch, but it could be a schedule, a pull_request, or an issue creation, or many other events.
More information about the GHA Workflow syntax.
Environment variables
Optionally, you can set environment variables for your next following steps.
Job definition
In this part, we set the name of our job: terraform, and configure it to run on GitHub virtual-environments using ubuntu-latest.
Checkout of Git repository
With this common GHA, we are doing a git checkout of the entire git repository.
Get AWS Credentials
To follow the least privilege mantra, I’m using a simple assume role and not directly IAM User credentials. This is possible thanks to this official AWS GHA: configure-aws-credentials.
Nb: AWS IAM action sts:TagSession was missing in my IAM Role policy and in the trust policy.
|
|
As you can see, the majority of arguments will retrieve secrets from the GitHub Action secrets store. (In the settings of your GitHub repository)
Run standard shell command
In this step, I’m running basically AWS CLI commands.
Use standard GitHub Actions for ECR
Using the official AWS ECR Actions, you will be able to login, build, push & logout your Docker images on AWS ECR.
|
|
Terraform Init
To properly use Terraform commands, I’m using this official GHA from Hashicorp.
Using args: you can pass arguments at the end of init command.
|
|
Terraform Validate
Terraform Plan
|
|
Terraform Apply
For the apply step, I’m using an if conditional statement (only done when there are changes to deploy).
|
|
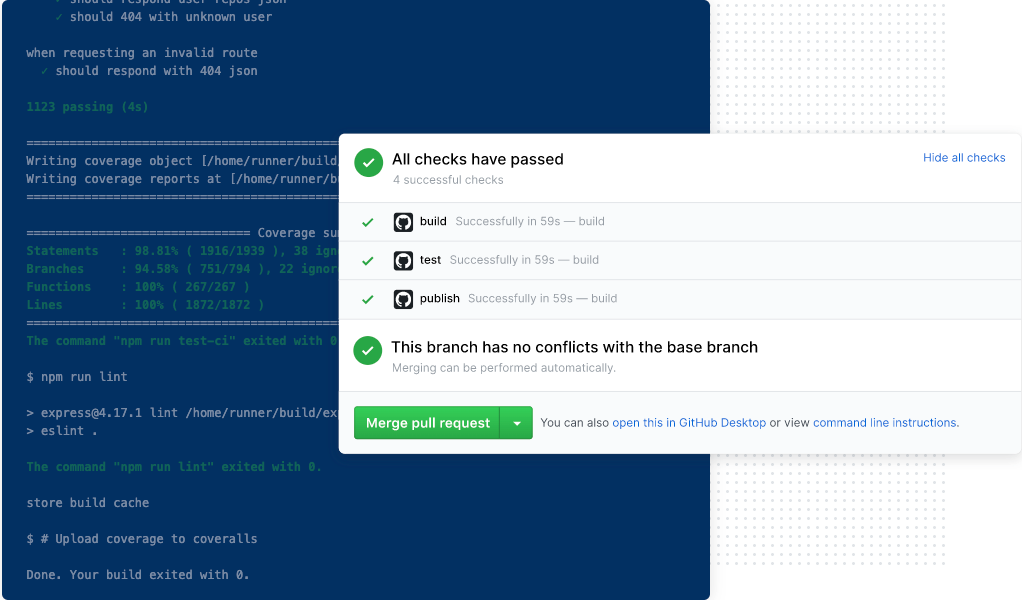
The final result is available here.
The overall maturity of the official Hashicorp GitHub Actions is pretty nice, with great documentation and examples. 👏
Using CloudFormation (SAM)
I’m voluntarily skipping the first part: name, job definition, env vars, checkout, and AWS credentials, as it’s the same as the previous Terraform example.
Test your credential
I’m using this simple command, equivalent to whoami on AWS CLI to check which IAM Role I’m using.
Build
For my sam use case, I’m using this Action found on the Marketplace from TractorZoom, as AWS does not provide any equivalent official GHA yet.
Deploy
In the deploy step, I need to pass some args. Some need to be set at the end without a carriage return, otherwise it fails.
|
|
💵 How much?
GHA minutes are free for public repositories. With a maximum of 20 concurrent jobs for the free tier.
For GitHub private repository:
- Free for 2,000 minutes per month (nearly 1 hour per day)
- After free tier: $0.008 per minute (Linux - 2 cores, 7GB)
Conclusion
✅ Good Points
- Large community; lots of examples available; See inspiration on many
.github/workflowfolders on public repositories. - Nearly infinite possibilities (2938 actions available on GH Marketplace):
- Caching Artifacts
- Slack, Discord, Telegram, Email CI/CD notifications
- Labeler: https://github.com/actions/labeler
- etc.
- You can run simple recurring/one-time batch scripts with the
on-scheduleevent.
❌ Improvement Points
- Sometimes, error messages are awful:
Technical information (for administrator): SQL Server Error: 4011 - Lack of official GitHub Actions from different vendors.
- Too many duplicated Actions on Marketplace; can’t sort by star ⭐️, we need more filtering capabilities.
- Missing global secrets/environment variables: I want to set some secrets or envs at the GitHub account level, not at the repository level.
Advanced use cases

- Terraform Advanced Example:
- Great blog-post about GHA: here.
That’s all folks!
zoph.